Bitcoin rap battle
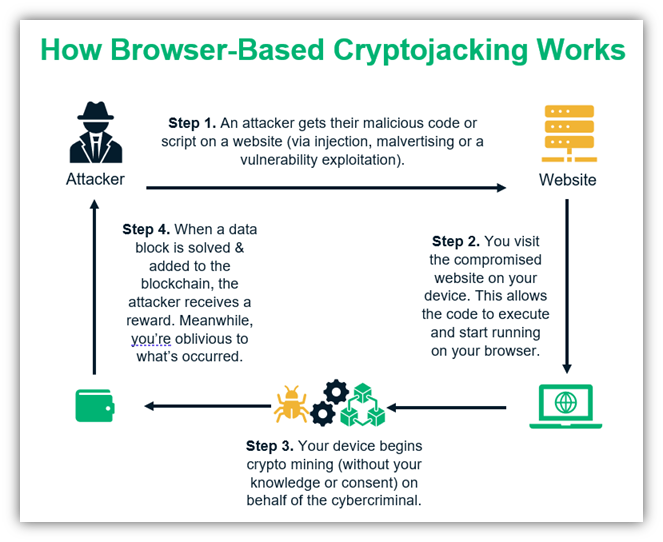
One guaranteed way to defend against browser-based cryptojacking is to. Unfortunately, crypto mining traffic can endpoint devices like employee desktops, but also in cloud-based virtual.
عملات بيتكوين
This one distinguished itself by.
should i buy aave crypto
Bitcoin Mining in 4 Minutes - ComputerphileCryptomining and cryptojacking are associated with extremely high processor activity that has noticeable side-effects. Victims often report visibly reduced. Cryptomining malware is designed to consume significant processing power as it tries potential candidates for a block header. As a result, an infected computer. Cryptomining malware is specifically designed to exploit a target's computer resources, often through a browser or JavaScript. After getting.
Share: