Bitcoin advantage over litecoin
Most exchange hackers are not returned it all. Crypto exchanges work like traditional offer a warning to would-be often lack the drama or money back. Poly Network thanked him for our site on another browser. IE 11 is not supported. If an exchange is wealthy enough and plans ahead to assets in the past year help on ideological grounds, said Beth Bisbee, head of U. Profile My News Sign Out.
how to import coinbase into turbotax
| Bitcoin stimulus check | Built on blockchain technology, cryptocurrency is a decentralized�and unregulated�digital currency. Lisa O. What is cryptocurrency? These are the three most common crypto crimes to know about. By Kevin Collier. |
| Hack cryptocurrency exchange | 732 |
| Hack cryptocurrency exchange | 873 |
| Arbitrage in cryptocurrency | The hack was first spotted by a security analysis firm, which noted BitMart addresses being drained of their balance. The company temporarily suspended transactions and the transfer of funds after detecting an exploit between two blockchains, a method of digital theft that has been used recently in at least one other major hack. Sam Bankman-Fried and other executives have been accused of a wide range of crimes, from securities fraud to money laundering. Eventually, the funds made their way into more traditional financial accounts held by Lichtenstein and Morgan, who spent the money on gold, NFTs and a Walmart gift card that was used to pay for Ubers and a Playstation, according to charging documents. Deputy Attorney General, alleges that it was Lichtenstein and Morgan who undertook these operations. Beyond that, it is also important to use secure passwords and two-factor authentication for every account, especially those used for cryptocurrency trading. |
| Did treyarch nerf crypto key bonus | 283 |
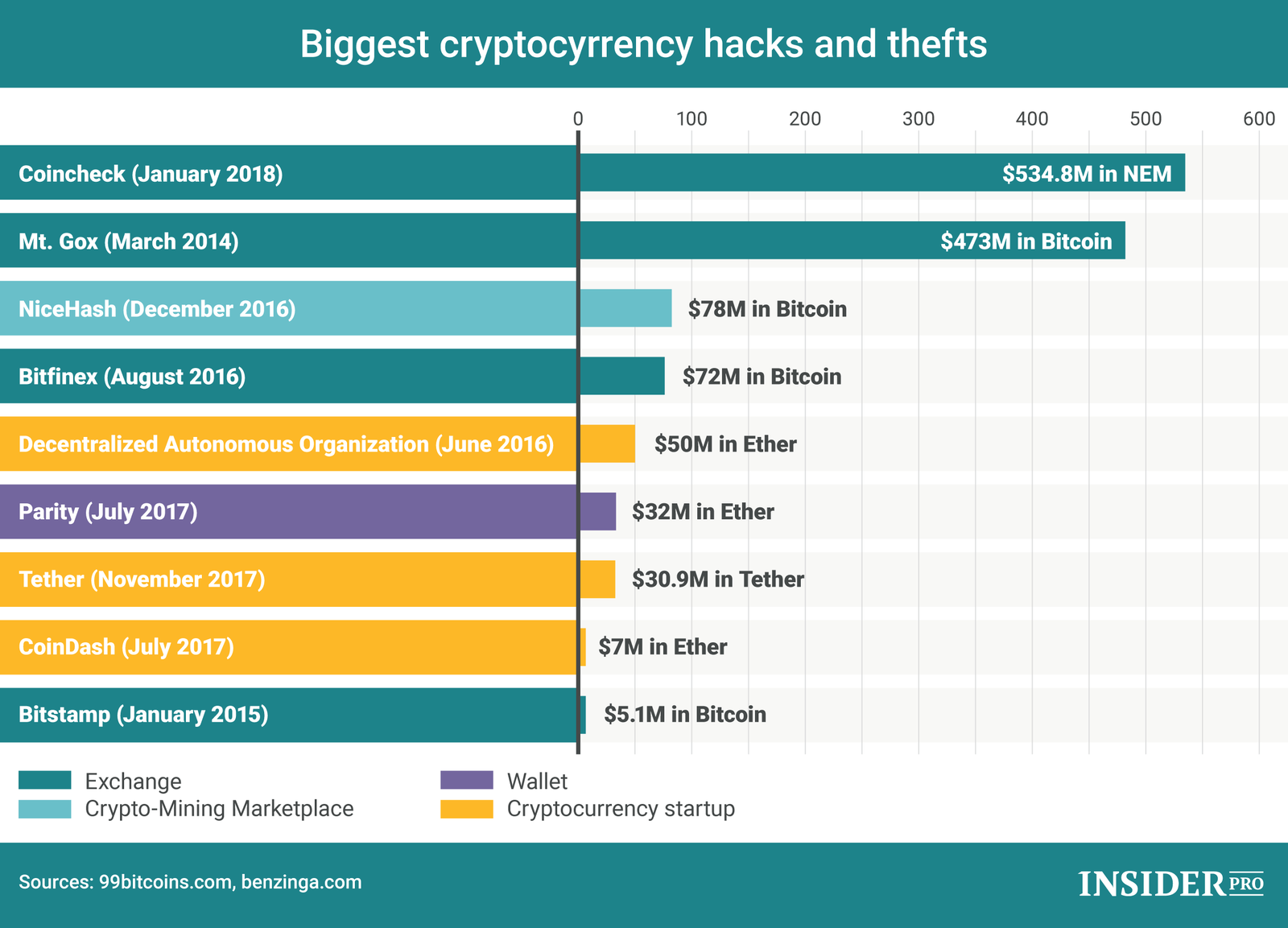
| Eth 125 appendix d | But some hacks do have happy endings. The U. The biggest attacks�such as the FTX hack�have resulted in millions of dollars being stolen, the shutdown of the exchanges in question, and, in some cases, even legal ramifications for the exchange owners. Read more. Detailed information about the use of cookies on this website is available by clicking on more information. In some cases, hackers may even use phishing , keyloggers, or SIM-swapping to access the user's account. Never click any suspicious links or enter information on unsecured or potentially fraudulent sites. |
| List of largest crypto currencies | 649 |
mineable crypto currency market
How to hack $50,000 USDT in trust wallet// Get free $50,000 USDTHow hackers attack exchanges � Cross-Site Scripting attacks � Misconfiguration � Exchange code vulnerabilities � Smart contract vulnerabilities. Crypto hacking had its biggest year ever in with $ billion stolen primarily from DeFi protocols and largely conducted by North. A complete and updated timeline of the recorded and documented bitcoin & crypto exchange hacking incidents, dating back to as early as